Public S3 Bucket!
S3 Data Leak? Your Incident Response Checklist! #shorts
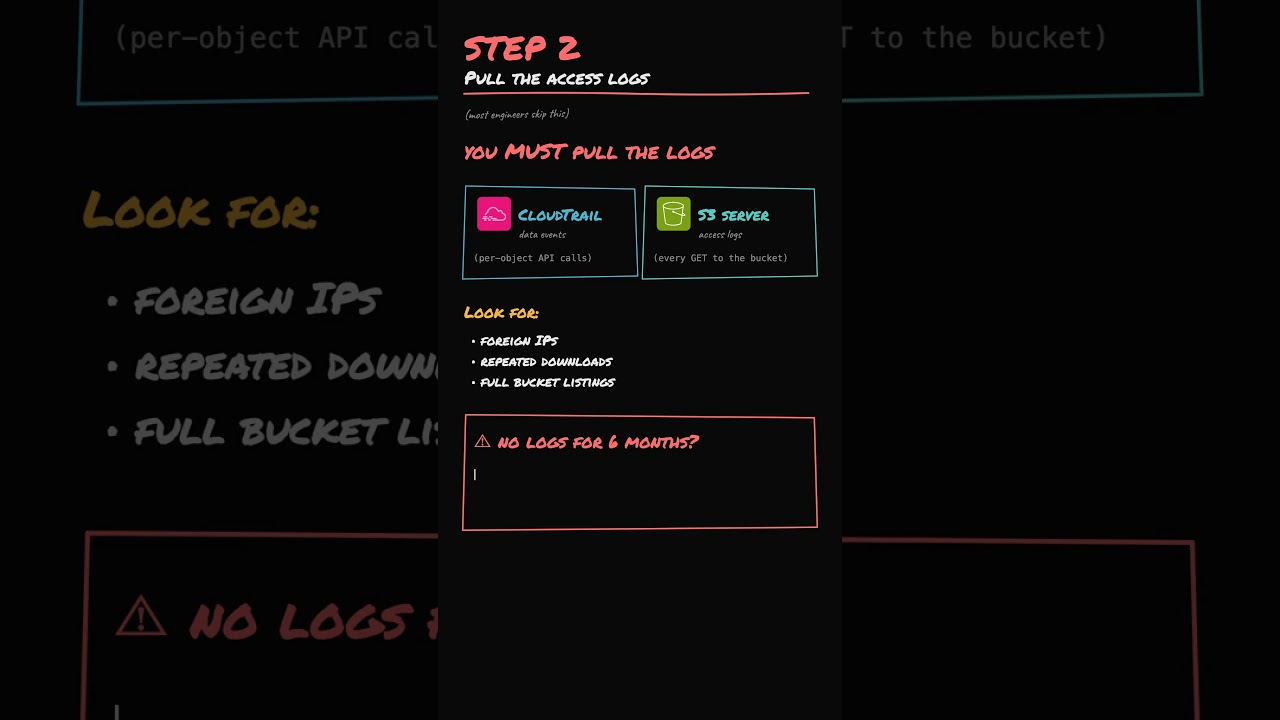
Securing a leaked S3 bucket is just the beginning of a critical incident response process. Immediately lock down the bucket using S3 Block Public Access at the account level and enable default encryption to protect the remaining data. You must then conduct a forensic analysis using CloudTrail and S3 Server Access Logs to identify unauthorized downloads; crucially, if logging wasn't enabled during the exposure, you must assume a confirmed breach occurred.
Beyond the technical fix, involve your legal and security teams immediately to address compliance mandates like the GDPR 72-hour notification window. To prevent a recurrence, enforce Service Control Policies (SCPs) at the AWS Organizations level to block public access globally and deploy AWS Config rules to automatically flag unencrypted or exposed buckets.
#AWS #S3 #CyberSecurity #IncidentResponse #CloudSecurity #InfoSec #GDPR #AWSConfig #CloudTrail #DataBreach #DevOps #TechTips #Compliance
Securing a leaked S3 bucket is just the beginning of a critical incident response process. Immediately lock down the bucket using S3 Block Public Access at the account level and enable default encryption to protect the remaining data. You must then conduct a forensic analysis using CloudTrail and S3 Server Access Logs to identify unauthorized downloads; crucially, if logging wasn't enabled during the exposure, you must assume a confirmed breach occurred.
Beyond the technical fix, involve your legal and security teams immediately to address compliance mandates like the GDPR 72-hour notification window. To prevent a recurrence, enforce Service Control Policies (SCPs) at the AWS Organizations level to block public access globally and deploy AWS Config rules to automatically flag unencrypted or exposed buckets.
#AWS #S3 #CyberSecurity #IncidentResponse #CloudSecurity #InfoSec #GDPR #AWSConfig #CloudTrail #DataBreach #DevOps #TechTips #Compliance
KodeKloud
...